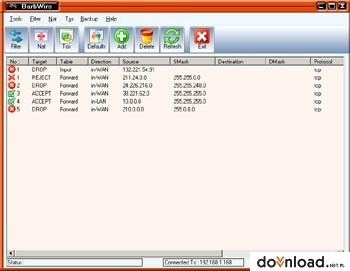
BarbWire Download
Filter
This is the place that we actually take action against packets and look at what they contain and DROP or ACCEPT them, depending on their payload. The filter table should be used for filtering packets generally. For example, we could DROP, LOG, ACCEPT or REJECT packets without problems as in the other tables. There are three chain built in to this table.
The first one is named FORWARD and is used on all non-locally generated packets that are not destined for our localhost (the firewall, in other words).
INPUT is used on all packets that are destined for our local host (the firewall) and OUTPUT is finally used for all locally generated packets.
Nat
The nat table is used mainly for Network Address Translation. . The PREROUTING chain is used to alter packets as soon as they get in to the firewall.
The OUTPUT chain is used for altering locally generated packets (ie, on the firewall) before they get to the routing decision.
Finally we have the POSTROUTING chain which is used to alter packets just as they are about to leave the firewall.
Mangle
This table is used mainly for mangling packets. We could change different packets and how their headers look among other things. The table consists of two built in chains, the PREROUTING and OUTPUT chains.
PREROUTING is used for altering packets just as they enter the firewall and before they hit the routing decision. OUTPUT is used for changing and altering locally generated packets before they enter the routing decision. Note that mangle can not be used for any kind of Network Address Translation or Masquerading, the nat table was made for these kinds of operations.
Here is an example of what can be done with barbwire.
For instance, 24.226.215.66 pings(ICMP) 24.226.215.67, you have two options that you can do on the firewall. Either you configure it to DROP that packet, which in this case no message will be returned to the requester or you can REJECT the request, which in this case the requester will have a network unreachable response.